Curated Images
What is a "curated image"?
We are dedicated to providing a simpler path for the TAMU community to access and use cloud resources. This philosophy has led us to develop an operating system image that can be selected by users that is preconfigured for some of the TAMU Security controls and has required software already pre-installed. This process is repeated on a regular basis and results in images that contain the latest patches and software versions.
Why use a curated image?
Within each of the public cloud providers, there are thousands of choices for types and configurations of operating systems, even within a single operating system choice like Ubuntu Linux. It can be overwhelming for users to choose a trustworthy source for an operating system image, and many images come with additional costs and requirements.
Once a user selects an operating system from the list, patches and security configurations must be applied to reduce vulnerabilities and meet security policies. This process may take a few minutes to an hour or more depending on the technical ability of the user.
AIP uses source images from the official providers of each operating system to ensure safe and reliable results during the curation process. The curated image provides users a starting point that is consistent and near production ready.
What are the benefits of the curated images?
- Basic security compliance settings that meet much of the TAMU Controls Catalog requirements
- Installs the Crowdstrike Agent as the antivirus software
- Installs the Nessus Agent used by TAMU IT Security for scanning and reporting of system vulnerabilities
- Azure Active Directory authentication for some Linux platforms to allow NetID login to the Linux operating system
- Saves the user the time they would have spent doing the above work themselves
- Provides consistency in configuration and software installed
See here for more detailed technical information about the curation process and security compliance.
How do you use the images?
Note: These images are not maintained by AIP or the cloud provider once set up. It is the responsibility of the resource owner to maintain appropriate patching schedules, software updates, and security compliance appropriate for the data classification, and to perform an annual risk assessment on all resources.
Curated images are available in Amazon and Azure for Ubuntu 18.04, 20.04, and CentOS 7. An image for Windows Server is in progress.
Using curated images in AWS
* Log into the AWS console at <https://aggie-innovation-platform.awsapps.com/start#/> and select the account in which to set up the new EC2 instance.
* Navigate to EC2 Instances and click `Launch instances`.
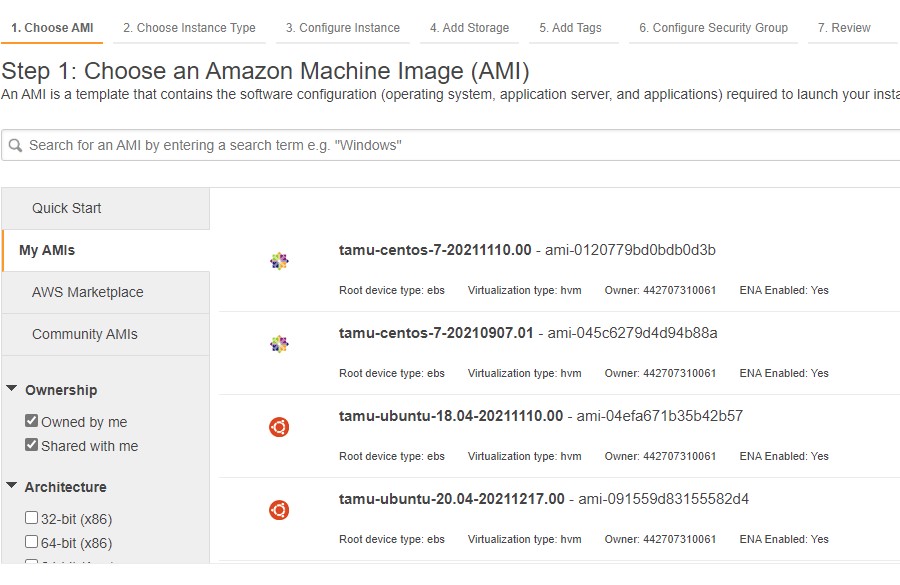
* Click `My AMIs` in the left column menu.
* Check the box `Shared with me` in the left column, the AIP images will populate as shown below and will always be owned/published from account # 442707310061
* Naming convention is tamu-os-version-creationdate.dailyversion.
* Click the `Select` box to use the desired image.
# Use the latest image in a series (recommended)
data "aws_ami" "tamu_ubuntu_2004" {
most_recent = true
owners = ["442707310061"] # AIP
filter {
name = "name"
values = ["tamu-ubuntu-20.04-*"]
}
}
resource "aws_instance" "example" {
ami = data.aws_ami.tamu_ubuntu_2004.id
instance_type = "t2.micro"
}
# Or, use a specific build
resource "aws_instance" "example" {
ami = "ami-033a34bf9eddca324" # tamu-ubuntu-20.04-20220411.00
instance_type = "t2.micro"
}
# Images will be owned by account number `442707310061`. You can use the AWS CLI to find all images published by AIP:
$ aws ec2 describe-images --owners 442707310061
# Or, filter by a specific image series:
$ aws ec2 describe-images --owners 442707310061 --filters "Name=name,Values=tamu-ubuntu-20.04*"
# Find the latest tamu-ubuntu-20.04 image
$ AWS_AMI_ID=$(aws ec2 describe-images --filters "Name=name,Values=tamu-ubuntu-20.04*" --query 'Images[0].ImageId' --output text)
# Launch a single instance
$ aws ec2 run-instances --image-id $AWS_AMI_ID --instance-type t2.micro --count 1
Using curated images in Azure
* Log into the AWS console at <https://portal.azure.com/>.
* Navigate to Virtual machines and click `Create`.
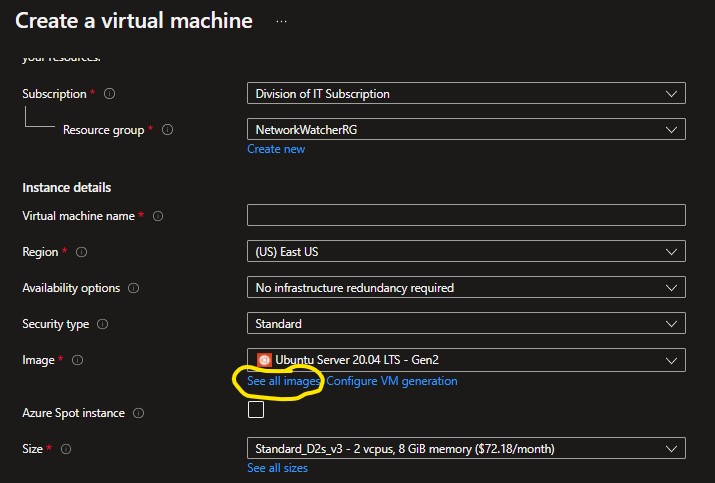
* Select your Subscription and Resource Group and fill in remaining details as needed.
* In the VM form, click `See all images` as shown below.
* Click on `Shared Images` on the left column under "My Items" the AIP images will populate. Naming convention is tamu-os-version.
# The terraform argument `source_image_reference` is not compatible with Compute Gallery images (only Marketplace images), but you can still use both the latest or a specific image in a series by omitting or including a version in the image ID.
resource "azurerm_linux_virtual_machine" "example" {
# The latest image in a series (recommended)
source_image_id = "/subscriptions/1d34f87a-203a-4c48-9422-af9a1f2d3f1f/resourceGroups/image-sharing/providers/Microsoft.Compute/galleries/TAMUsharedImageGallery/images/tamu-ubuntu-20.04"
# Or, a specific version
source_iamge_id = "/subscriptions/1d34f87a-203a-4c48-9422-af9a1f2d3f1f/resourceGroups/image-sharing/providers/Microsoft.Compute/galleries/TAMUsharedImageGallery/images/tamu-ubuntu-20.04/versions/20220422.00.0"
}
# Use the Azure CLI to list all images and versions published by AIP:
$ az sig image-definition list --subscription 1d34f87a-203a-4c48-9422-af9a1f2d3f1f --gallery-name TAMUsharedImageGallery --resource-group image-sharing
# Or only for a specific image series:
$ az sig image-version list --subscription 1d34f87a-203a-4c48-9422-af9a1f2d3f1f --gallery-name TAMUsharedImageGallery --resource-group image-sharing --gallery-image-definition tamu-ubuntu-20.04
# Create a new virtual machine using the latest tamu-ubuntu-20.04 image:
$ az group create --name myResourceGroup --location southcentralus
$ az vm create --resource-group myResourceGroup \
--name myVM2 \
--image "/subscriptions/1d34f87a-203a-4c48-9422-af9a1f2d3f1f/resourceGroups/image-sharing/providers/Microsoft.Compute/galleries/TAMUsharedImageGallery/images/tamu-ubuntu-20.04"
Using curated images in Google
Curated images are not available in Google Cloud at this time, it is planned for the future.
Image details
For the most recent information on package details or for access to the image pipeline, contact AIP at aip@tamu.edu
| OS | Compliance Report | Installed Packages | Build Log |
|---|---|---|---|
| centos 7 | ComplianceAsCode v0.1.59.2 | Package list | Build log |
| ubuntu 18.04 | ComplianceAsCode v0.1.59.2 | Package list | Build log |
| ubuntu 20.04 | ComplianceAsCode v0.1.59.2 | Package list | Build log |
* Requires an upcoming feature release to CSI. Scan results can be sent to you by request: secassessment@tamu.edu